Securing Smart Devices
With the ability to interact with the user, connect to other peers, and sense the environment, smart devices, including the mobile device, wearable, and Internet-of-Thing (IoT) device, have enabled a plethora of promising applications. From daily mobile payment to personal healthcare monitoring, smart devices have penetrated into every part of our life.

Along with the great convenience of smart devices, there also comes an increasing concern about their security issues, as the data involved is often extremely valuable and highly sensitive, gaining much attention from malicious attackers. Also, the limited computing resource, growing data transmission capability and expanding device-device connectivity have aggravated the security threats.
As a result, securing the ecosystem of smart devices has attracted a great deal of attention from both academia and industry. Among the research pioneers is Prof. Qian Zhang, who envisioned many years ago that great potential and serious threats coexist in smart devices. One major research of Prof. Zhang's group in HKUST is to build reliable and robust securing systems for smart devices, including the following aspects:
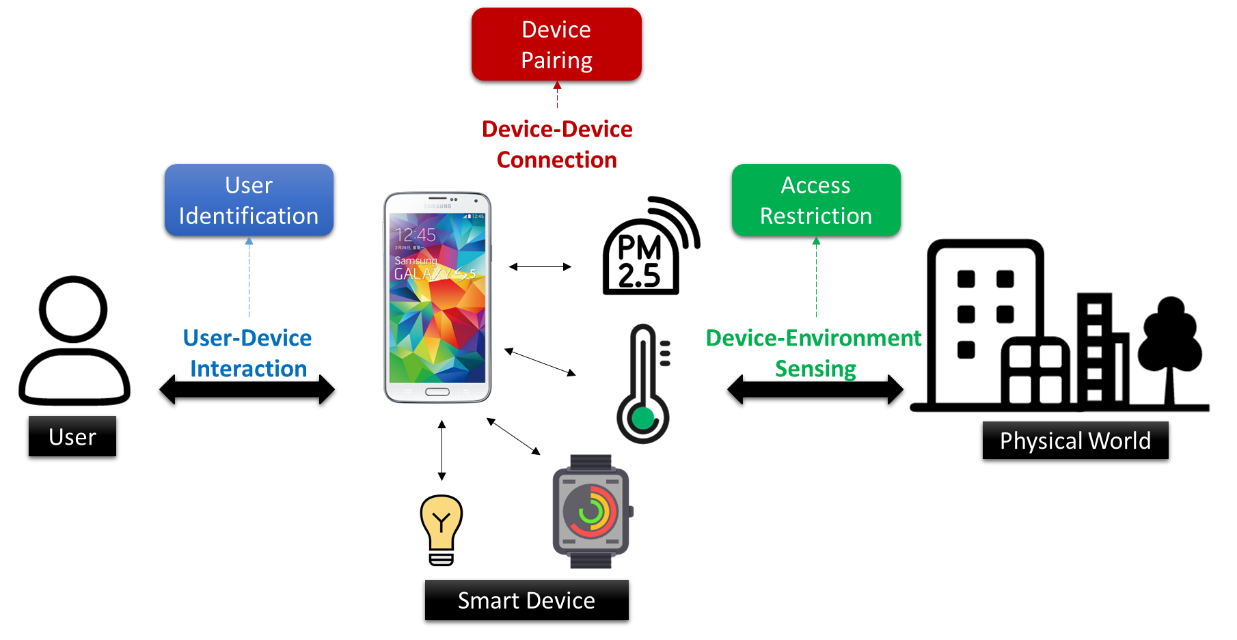
(1) User-device interaction defines how the user accesses the device. From the perspective of security design, Prof. Zhang's group focuses on recognizing who is using the smart device. Existing user identification solutions either rely on expensive hardware, e.g., fingerprints, or require complex modeling and large computation power. As both the computation and battery are scarce resources on many smart devices, existing solutions do not work well. To fill the gap, Prof. Zhang's group builds two light-weight user identification systems for power-constrained devices. One uses the underlying pattern hidden in the human gesture dynamics as an identifier while the other one leverages the bio-vibrometry, i.e., the vibration response of the human body, to differentiate various users. According to their comprehensive evaluations on the volunteers, both systems can provide identification accuracy above 91% in small-scale scenarios of limited users (e.g., home scenario) with minimal power requirement and are robust to various confounding factors.
(2) Fueled by the close cooperation among smart devices, the device-device connection is prevalent and forming secure pairing between devices lays the foundations of the security protection and data privacy preservation. Prof. Zhang's group has devoted much effort in this field and successfully built several systems, each of which targets different scenarios and provides various security levels. Touch-And-Guard (TAG) is their first research outcome. It uses hand touch as an intuitive means to establish a secure connection between a wristband wearable and the touched device. Specifically, it generates secret bits from hand resonant properties and uses it to authenticate each other and then communicate confidentially. The evaluations on 12 volunteers indicate that TAG can serve as a natural and user-friendly pairing interface by generating secret bits at a rate of 7.84 bit/s, 58% faster than conventional text input PIN authentication.
Apart from that, a proximity-based mechanism with a better security level, Move2Auth, is also proposed. In Move2Auth, a user only needs to hold the smartphone and perform random rotations in front of the IoT device. As the rotations lead to significant variations and fast changes in signal attenuation and antenna polarization, a secure and random key can be extracted from the Received Signal Strength (RSS). By matching the RSS-trace and motion data captured by the built-in motion sensors on the smartphone, Move2Auth can create a secure link between these devices and can protect against a powerful active attacker who can arbitrarily tune transmission power.
To further boost the security level, the research group also explored the possibility of secure pairing based on human bio-metrics: the Electromyogram signal (EMG) caused by human muscle contraction. By exploring stochastic nature hidden in the EMG signal to generate secure bits, their work proves that the secure key generated from the EMG signal has sufficient randomness and security--even when the attacker can perfectly copy the user's gesture, the generated secure key cannot be stolen or cracked. Extensive evaluation on the volunteers under different scenarios demonstrates that this system can achieve a competitive bit generation rate of 5.51 bit/s while maintaining a very high-security level. Also, the evaluation results with the presence of adversaries demonstrates that their system is very secure to strong attackers who can eavesdrop on proximate wireless communication, capture, or even imitate the legitimate pairing process with the help of advanced computer-vision-based techniques.
(3) In the context of device-environment sensing, Prof. Zhang and her group members have explored the possible security attacks caused by the continuous, unobtrusive, and unrestricted sensing ability of mobile devices. They first investigate how to prevent mobile-camera-based piracy attack on physical intellectual properties, such as painting and sculpture. To this end, a new lighting system, Rainbow, is invented to pollute the pirate photo/video on the mobile camera but retains a good visual quality for the human observer. By carefully modulating the chromatic change and luminance flicker into the light system, Rainbow introduces a non-uniform variation into the reflected light energy from physical objects, thus maximizing the distortion caused by the camera's banding effect. Meanwhile, due to the color fusion ability and low-band pass characteristics of human vision, the visual quality for the human observer is not affected. Extensive objective evaluations under different scenarios indicate that this lighting system is robust with different confounding factors and can significantly pollute the piracy photos on various devices.
After that, another potential but serious information leakage attack is also exhibited by demonstrating how the attacker can unobtrusively track users in an indoor scenario. The key is to explore the nonlinearity characteristics of the ambient light sensor to sense the high-frequency modulated location information with a low sampling rate. In particular, due to the nonlinear characteristics of electronic components inside the circuit, the amplifier in ALS exhibits some levels of nonlinearity. When two high-frequency signals are received by the ALS simultaneously, such nonlinearity renders the output signal of the amplifier violate the linear superposition rule and generate a low-frequency "shadow" signal. In light of this idea, the research group has built a low-power and unobtrusive indoor localization system, NALoc. The experiments on ALS sensors from Apple and Samsung devices confirm the feasibility of such a system and extensive experiments demonstrate that it is possible to derive the fine-grained location information unobtrusively from the ALS readings, which poses a brand-new security threat. Corresponding countermeasures are also discussed in their research paper.





 Facebook
Facebook LinkedIn
LinkedIn Instagram
Instagram YouTube
YouTube Contact Us
Contact Us