Pushing the Limit of IoT Sensing
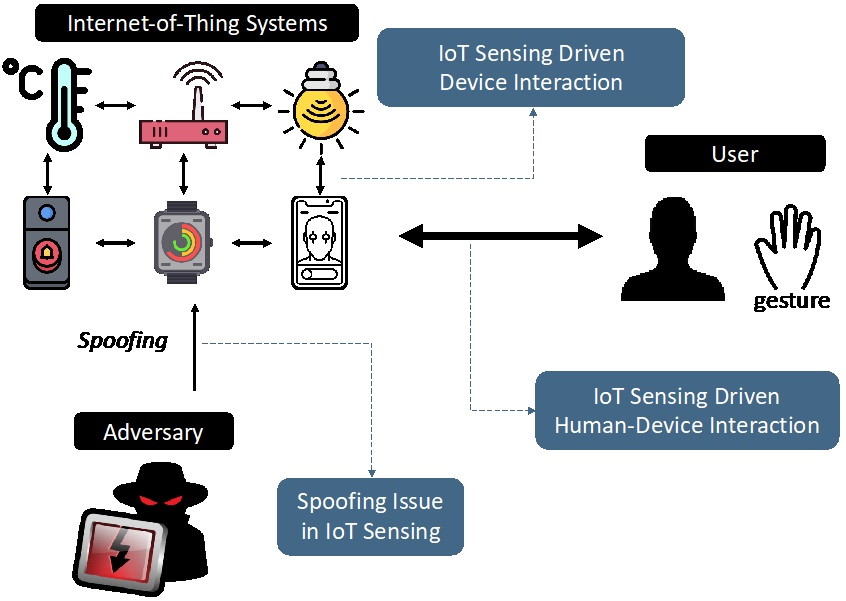
The past decade has witnessed the rapid penetration of smart Internet-of-Thing (IoT) into our daily life. It is estimated that, by the end of 2020, the number of connected IoT devices will be 20.8 billion. Sensing is one of the core functions of IoTs to bridge digital space and physical world. For example, the smart sensors automatically monitor our living environment, so that the digitalized data facilitate analysis and further action to maintain livable surroundings; the wearable devices continuously track our physical states so as to quantify our health conditions. With sensing capability, smart IoTs can collaborate together and empower a plethora of promising applications. However, compared with the explosive growth of IoT devices, the market of IoT sensing applications is still in its infancy and far from maturity.
As a result, enhancing the capability of the IoT sensing ecosystem has attracted a great deal of attention from both academia and industry. Among the research pioneers is Prof. Qian Zhang, who envisioned many years ago that great potential of IoT sensing. One major research of Prof. Zhang's group in HKUST is to design and build reliable and practical systems to explore the potentials of IoT sensing, including the following aspects:
(1) IoT sensing driven device interaction
Cooperation between IoT devices is key enabler to take advantage of each other's strengths so as to benefit upper-layer applications, i.e., on-body IoTs work with off-body devices in motion tracking systems, smart sensors work with access points in smart home applications. For IoT sensing applications, device tracking and identification are two cornerstones for device cooperation.
Device tracking provides the spatial relationship between different devices to facilitate numerous sensing applications such as interactions in VA/AR applications and location-based services. To enable device tracking in commodity IoTs, Prof. Zhang's group focuses on acoustic-based tracking solutions because many IoT devices such as smartwatch, smart speaker, VR glass have been equipped with supporting hardware, i.e., the speakers and microphones. Existing acoustic-based solutions generally adopt distance-based tracking, where distances between multiple speaker-microphone pairs are extracted for tracking. However, the achievable accuracy of such system depends on the separation between speakers, i.e., a large speaker array brings better performance but also makes it impractical to apply on IoT devices with small form factor. To fill the gap, Prof. Zhang's group proposes an angle-based motion tracking system, which greatly relaxes the requirement of a large speaker array. The system has two speakers playing single frequency tone to generate a periodically changed sound field. Then the microphone receives the sound and sense the change of the sound field. The system extracts the angle information from the sound field and distance information from single frequency tone to enable fine motion tracking. The evaluation results show that the angle-based motion tracking system can achieve around 5cm tracking accuracy.
To realize reliable cooperation, device identification aims to identify transmission from other authentic IoT peers to enable reliable device cooperation. Traditional cryptography-based security protocols are generally too sophisticated and pressure most IoTs with minimalist design and limited resources. Instead of using complicated security protocols. Prof. Zhang's group develops a lightweight scheme to extract physical-layer signatures embedded in pilot sub-carrier signals to protect IoT devices from active attacks. These signatures can be regarded as the sensing output of multi-path wireless radio environment around the IoT devices, which is unique in terms of device location (within half-wavelength of carrier frequency) and time (within wireless coherence time). In addition, they observe that pilot sub-carrier signals incorporate another dimension of information, transceiver-specific signatures due to manufacturing imperfections. Integrating both them can construct sensitive profiles to detect and mitigate active attacks. According to their comprehensive evaluations in typical indoor environments, the proposed system can mitigate 99.6% active attack attempts, only triggering false alarms on 3.1% of legitimate traffic.





 Facebook
Facebook LinkedIn
LinkedIn Instagram
Instagram YouTube
YouTube Contact Us
Contact Us